-
 Continue reading →: How to Manage Exchange Attributes Online Without an On-Premises Exchange Server?
Continue reading →: How to Manage Exchange Attributes Online Without an On-Premises Exchange Server?In this post I like to write about how you can manage Microsoft Exchange attributes while still maintaining a local Windows Server Active Directory but not using Exchange attribute writeback and going to get rid of the last Exchange Server. This is just an part of the journey to move…
-
 Continue reading →: Microsoft Build 2026
Continue reading →: Microsoft Build 2026The next Microsoft Build 2026 takes places, on June 2-3, 2026, live from San Francisco and online, bringing developers together around one clear theme: AI as the foundation of every product, workflow, and experience. The event centers on deep technical sessions, hands‑on labs, and direct access to Microsoft and GitHub…
-
 Continue reading →: Migrating Azure Storage Accounts for AudioCodes SBC Deployment from GPv1 to GPv2
Continue reading →: Migrating Azure Storage Accounts for AudioCodes SBC Deployment from GPv1 to GPv2Microsoft has announced the retirement of legacy general-purpose v1 (GPv1) storage accounts, requiring customers to migrate to general-purpose v2 (GPv2) by October 13, 2026. While this may sound like a simple backend change, some environments still rely on older deployments including virtual machines and network appliances that were originally provisioned…
-
 Continue reading →: Microsoft Teams Call Transfer Update
Continue reading →: Microsoft Teams Call Transfer UpdateMicrosoft Teams plans to roll out an updated call transfer experience for desktop users on Windows and macOS. The update focuses on speeding up transfers and making it easier for users to reach the right contact. There will be two buttons for each action one and new normal will be…
-
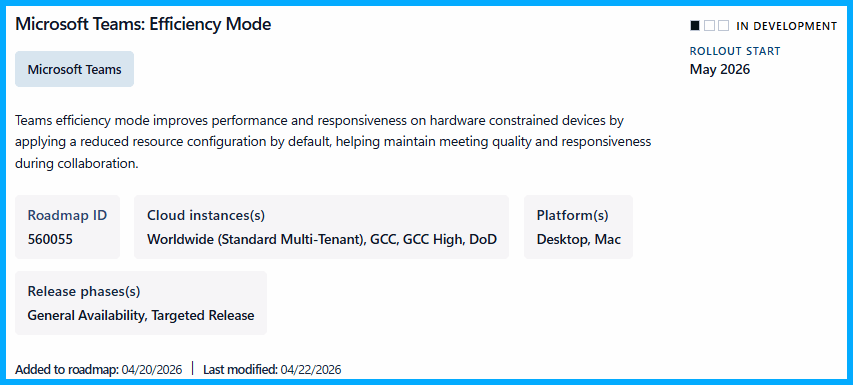 Continue reading →: Microsoft Teams Efficiency Mode
Continue reading →: Microsoft Teams Efficiency ModeIn this post I like to highlight the upcoming introduction of the so called “Efficiency Mode” which is aims to provide a smooth Teams User experience and keeping the experience more fluently on devices with limited hardware capacity. This should deliver a optimized performance and responsiveness for device with lower…
-
 Continue reading →: Microsoft Teams Call Queue App comes to mobile
Continue reading →: Microsoft Teams Call Queue App comes to mobileMicrosoft is expanding the Queues app in Microsoft Teams to mobile devices, enabling agents and supervisors to manage call queues directly from the Teams app on iOS and Android. This update brings essential call-handling capabilities to mobile-first and on-the-go workflows. With this update, Teams mobile users gain access to core…
-
 Continue reading →: Anthropic Models for Copilot on by default in Word, Excel, and PowerPoint
Continue reading →: Anthropic Models for Copilot on by default in Word, Excel, and PowerPointAlso very noteworthy to pay attention to new LLMs in Microsoft 365 Apps with Copilot. Also a fresh catch, telling that Anthropic Models for the apps are on by default, soon. Did you know? I did not. Microsoft message center notification MC1269241 tells the details. This change must not be…
Curated updates and insights on Microsoft Teams, Copilot, and Microsoft 365 for enhanced teamwork and productivity
Hello!
I’m Erik

Welcome to Erik’s blog, I post curated updates and insights on Microsoft Teams, Copilot, and Microsoft 365. Join me as we explore the latest developments, share valuable information, and spread knowledge. This blog not only serves as a source of news but also as my personal collection of notes, openly shared with you all. Let’s elevate teamwork and productivity together!
Let’s connect
📧 Subscribe
Stay updated and get the latest blog posts sent by mail to your inbox.