In this post I describe how you can configure safe attachments and safe links in Microsoft Office 365 Advanced Threat Protection (ATP) to make your communication and collaboration a more secure. It is for your Office 365 workloads (SharePoint Online, OneDrive for Business, Exchange Online and Microsoft Teams).
Please note, that is is just one of many measures to secure your communication and collaboration in Microsoft Office 365. This is only a single part – well, two capabilities – of a more holistic and required security architecture concept. Moreover, the below description, configuration etc. might change anytime and is just an example, demo piece.

Basics
Let me describe it as follows short and simplified:
What are Safe Links?
Safe Links are (hyper)links/urls which are pre-checked (in a sandbox) before a user opens the link. This “pre-check” is built to check if the website behind the link is ok or might be bad, start to download malware or something else which might harm your system/s.
What are Safe Attachments?
Safe Attachment[s] is a feature which checks attachments and tries to detect if it is malicious.
Requirements
You need a subscription which includes Microsoft [Office] 365 Advanced Threat Protection (ATP).
To configure this your administrative Office 365 account must have the global admin, security admin or Exchange Online Organization Management role assigned.
Configuration overview and walk-through
For both, you can start at https://security.microsoft.com/securitypolicies in the Microsoft 365 Security portal.
The following screenshots depict what I configured, so you can of course configure it another way depending on your needs and requirements.
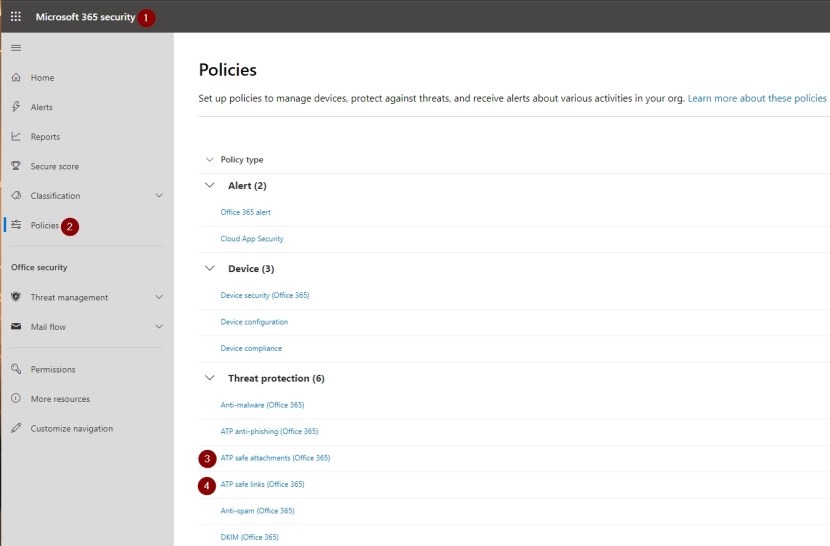
1 Open https://security.microsoft.com/securitypolicies
2 Policies
3 + 4 Configure each (ATP safe attachments + ATP safe links)
ATP Safe Attachments
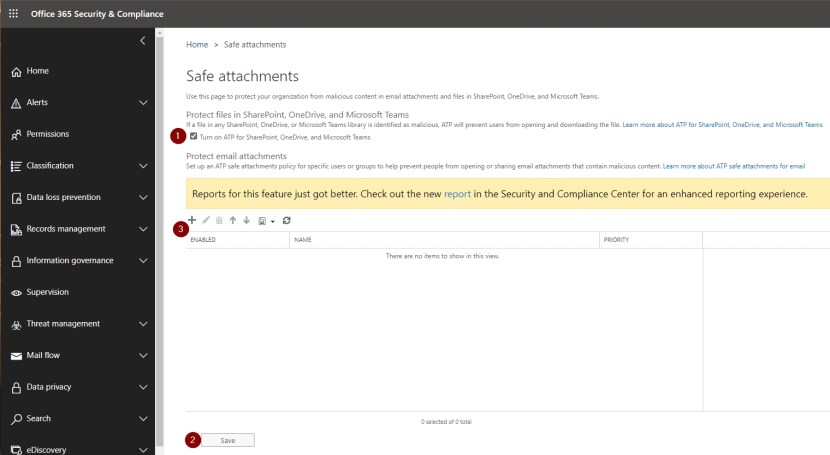
1 Enable ATP for SharePoint, OneDrive and Teams
2 Save it, to enable it
3 Protect attachments – create a new safe attachments policy
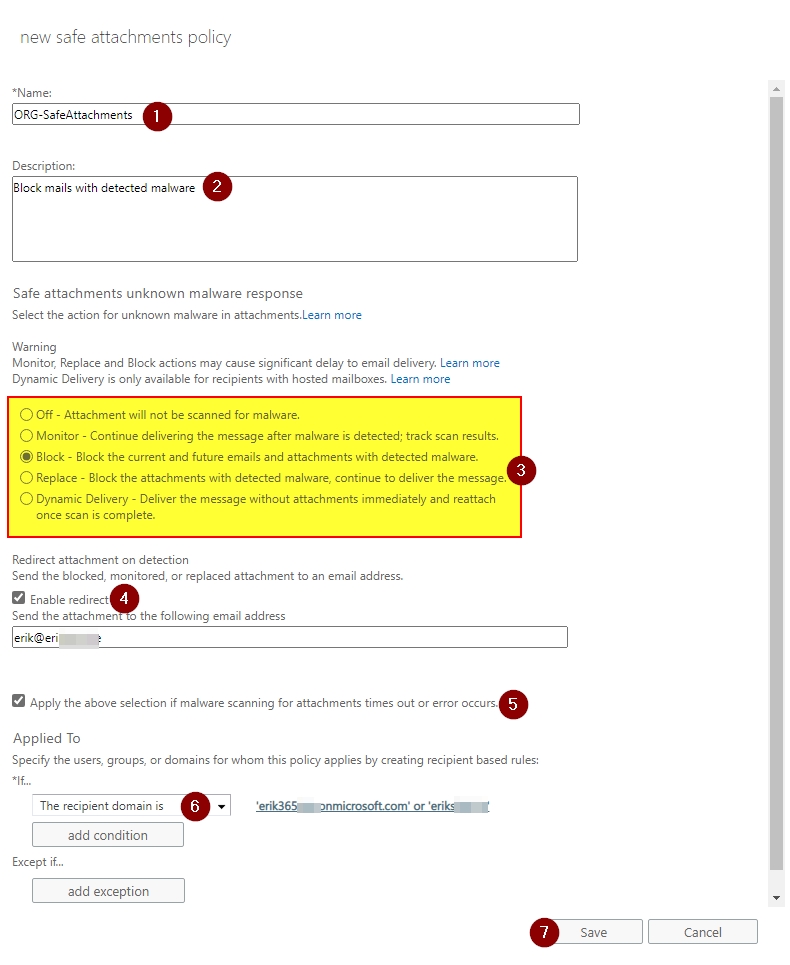
1 + 2 Give it a name + description
3 Configure handling
4 + 5 Enable redirect of potentially maliciouse attachements to another mail [don’t use a usual mailbox, create a “dumpster mailbox” just for that purpose]
6 Configure condition/s / exception/s
7 Save it
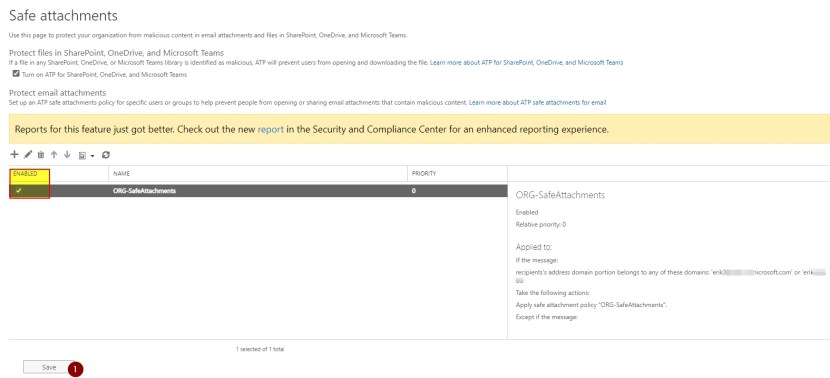
Validate input and check if the policy is enabled and the priority fits in case you create several policies.
ATP Safe Links
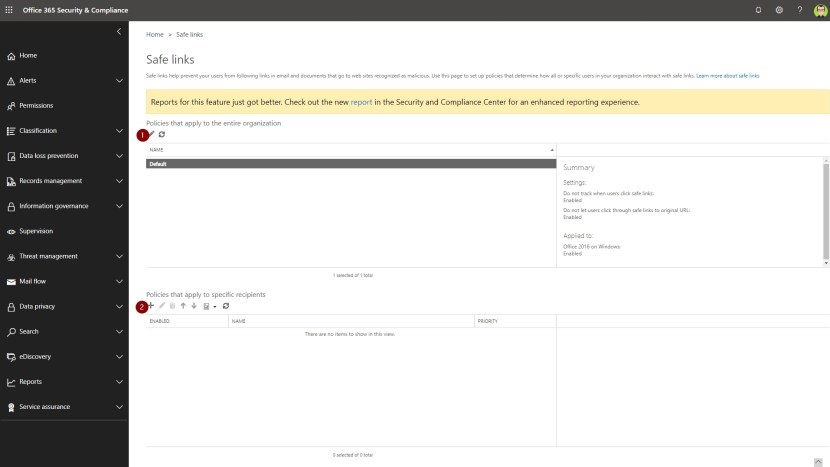
1 Configure the default Safe Links organization policy
2 Create Safe Link policies for specific recipients
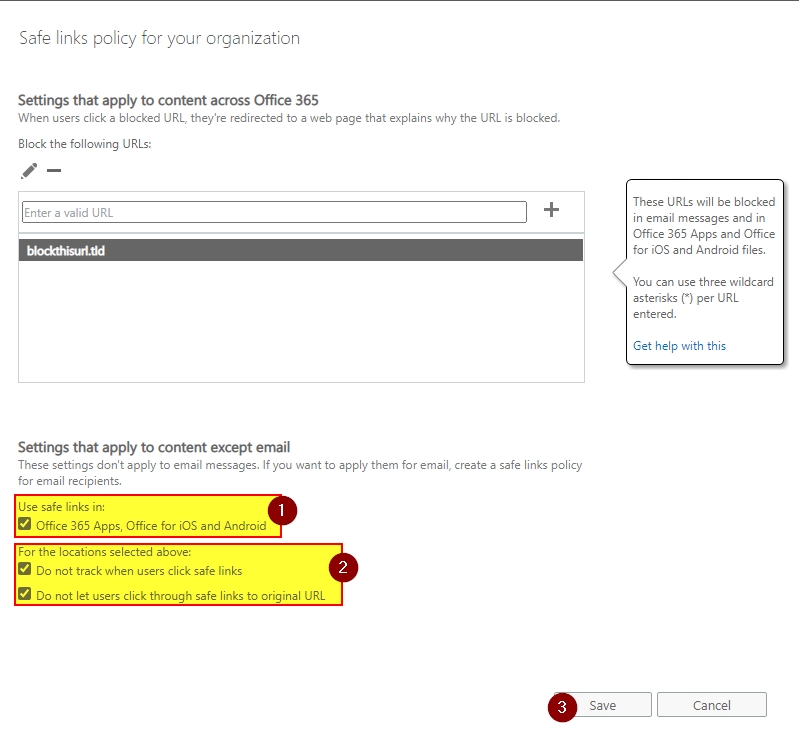
1 Enable it for all Office 365 Apps, … iOS and Android
2 Configure “reporting” + handling
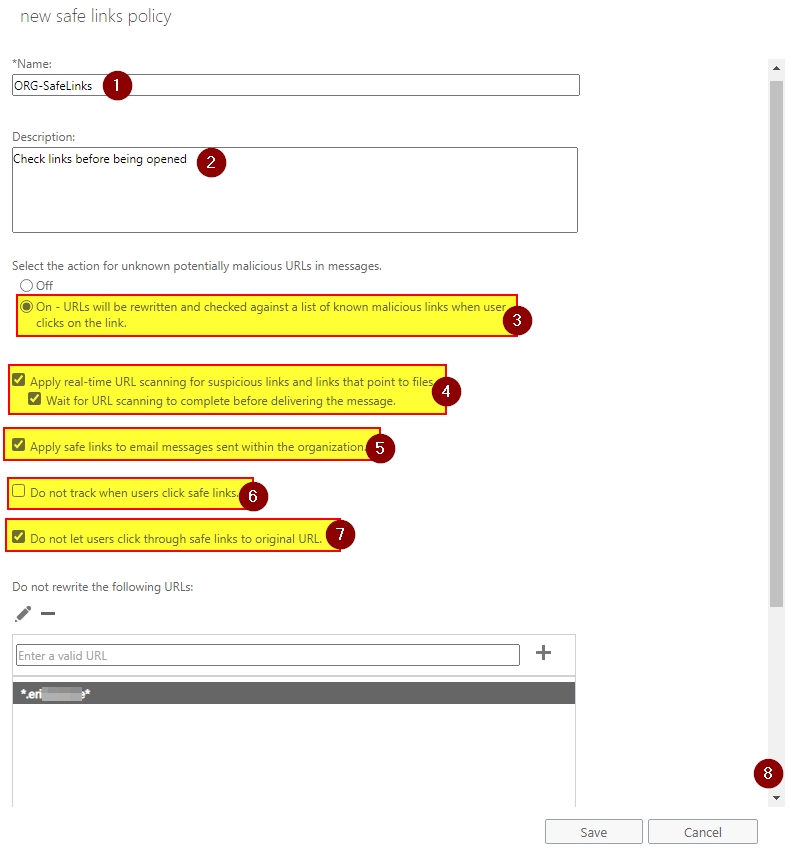
1 + 2 Give it a name + description
3 Turn it on
4 Enable real-time scanning for URLs including content for download
5 Enable it internally, too
6 Configure “reporting”
7 Enable – disables users to click the original URL from the warning page if it is blocked
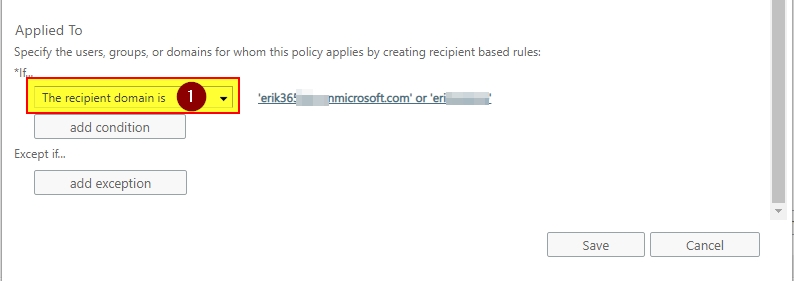
1 Configure condition/s / exception/s

Validate input and check if the policy is enabled and the priority fits in case you create several policies.
Finally, test and verify your configuration. Regularly take a look into your security reports to enhance your configurations. Plus, don’t forget from time to time to check out what has changed to keep your security configurations always at a current level.
Conclusion, opinion and summary
Safe Links and Safe Attachments are very helpful features in Microsoft Office 365 to make your communication and collaboration more secure regarding sending/receiving links and attachments. These two features are options to increase your security setup with Office 365. I think it might be a good idea to enable it if you do not yet have something like this in place already.
Although it makes links and attachments safe[r] there are more and more advanced/intelligent threats and approaches available to trick and compromise users and systems. So, admin and user security awareness is also essential although you can get rid of many threats with a holistic security architecture and technical solution or service implementations.
Update July 26, 2021
Safe Links in Microsoft Defender for Office 365 is generally available for tenants using both, Microsoft Teams and Microsoft Defender for Office 365.
Additional resources
- Office 365 ATP Safe Links
- How Office 365 ATP Safe Links works
- Office 365 ATP Safe Attachments
- How Office 365 ATP Safe Attachments works
- Office 365 Advanced Threat Protection service description
- https://techcommunity.microsoft.com/t5/microsoft-defender-for-office/microsoft-teams-gets-more-phishing-protection/ba-p/2585559 [added July 26, 2021]




Comment / Kommentar verfassen